as a result it would occur all the way down to your preferences regarding integration, like for those who’re a supporter of Google Maps or YouTube, for which Microsoft has minimal to contend with.
powerful Passwords: implement powerful password procedures. Require buyers to produce sturdy passwords, abide by security ideal practices, and keep away from clicking on suspicious links, to guard themselves from social engineering assaults.
LayerX is reason-constructed to provide security teams the correct resources info selanjutnya to safeguard clients and workforce inside of a cloud-initial landscape.
Battery drains swiftly. Malware can take in a substantial level of electrical power, resulting in your battery to empty more quickly than usual.
Should your iOS system is behaving unusually, you'll find two swift checks that will probably make it easier to detect the source of the problems:
Apple’s App Store is famously well-safeguarded, but there are still many malicious applications that sneak as a result of Apple’s safeguards.
It’s hugely unlikely, even though not unachievable, for an iPhone to get a virus since every iPhone app operates in its have Digital House. With iPhone applications running in virtual Areas, viruses can’t propagate.
A cross-web page scripting attack occurs when malicious javascript code is injected by way of a dependable Internet site into a person's browser. such a assault operates similarly to an SQL injection attack and preys on The shortcoming of browsers to differentiate between destructive and harmless markup text. Browsers simply just render whatever textual content they receive, despite its intent.
destructive written content safety: World-wide-web security blocks acknowledged-lousy phishing web-sites and drive-by downloads, and inspects World-wide-web traffic for destructive material. This aids to protect workers from malware together with other threats.
With both of those browsers functioning on Chromium, the general practical experience is remarkably identical now, and that makes the switch to Microsoft Edge a significantly less daunting one in case you’ve been among the lots of long-time Chrome buyers and are now thinking of changing.
Editorial independence implies being able to give an impartial verdict about a product or company, With all the avoidance of conflicts of fascination. to be sure this is achievable, each and every member of the editorial employees follows a clear code of carry out.
The definition of a virus is destructive software package that spreads by infecting other documents, normally corrupting details and crashing methods in the procedure.
more mature answers aiming to tackle the gaping security void of the public internet have all relied on sacrificial security. elaborate integrations spanning from Net proxies to cloud-primarily based isolation have included ever more additional body weight to straining user experience and security teams.
Some Apple buyers jailbreak their phones to bypass limitations and acquire more Charge of the iPhone operating technique. even so, jailbroken iPhones devoid of use of antivirus updates and security patches are noticeably fewer secure.
 Michael Bower Then & Now!
Michael Bower Then & Now! Tina Louise Then & Now!
Tina Louise Then & Now! Christy Canyon Then & Now!
Christy Canyon Then & Now!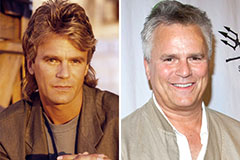 Richard Dean Anderson Then & Now!
Richard Dean Anderson Then & Now! Kerri Strug Then & Now!
Kerri Strug Then & Now!